Cybersecurity Risk in M&A: Assessing What You Are Really Buying
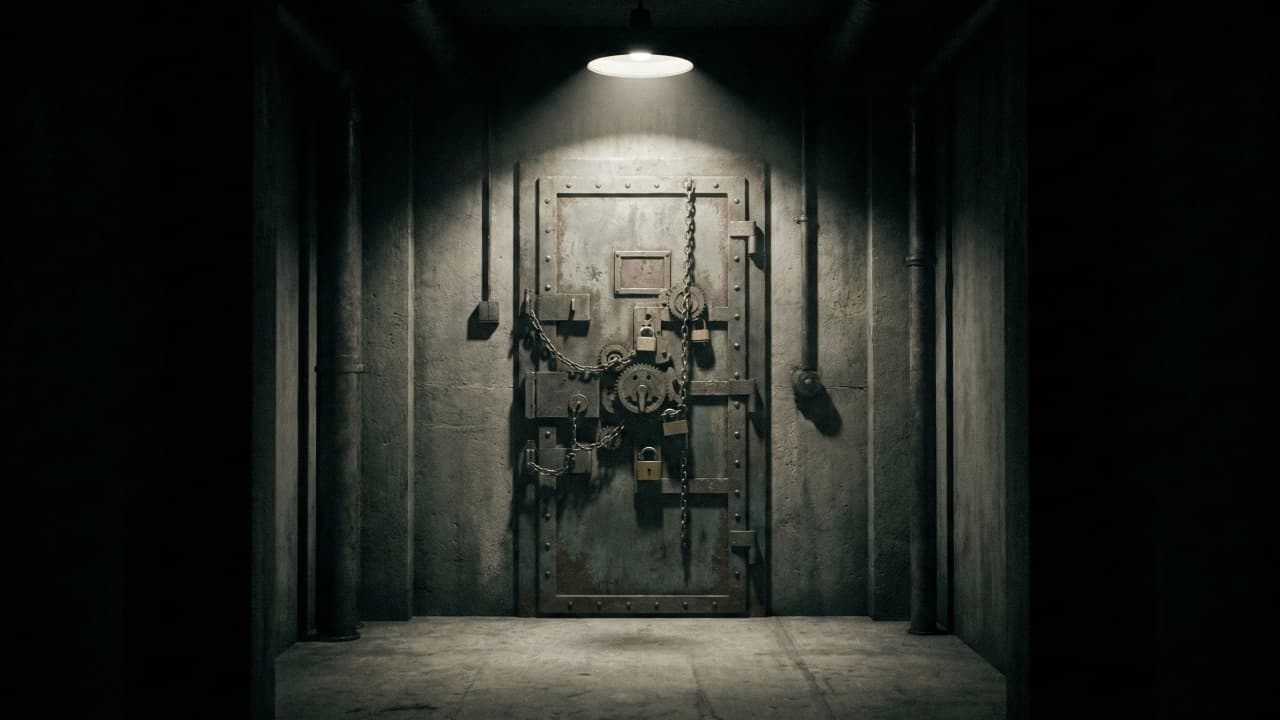
The Hidden Liability
Cybersecurity risk is one of the most consequential — and most frequently underassessed — aspects of M&A due diligence. When you acquire a company, you acquire its security posture, its vulnerability history, its compliance status, and any undiscovered breaches that may surface months or years later.
The examples are well-documented. Verizon reduced its Yahoo acquisition price by $350 million after data breaches were disclosed during due diligence. Marriott discovered that Starwood's reservation system had been compromised for four years after the acquisition — resulting in a $124 million GDPR fine.
What Security Due Diligence Should Cover
Security Program Assessment
Governance: Does the organization have a CISO or equivalent? Is there a security policy framework? Are policies reviewed and updated regularly?
Risk management: Does the organization conduct regular risk assessments? Are risks documented and tracked? Is there a risk acceptance process?
Incident response: Does the organization have an incident response plan? Has it been tested? What incidents have occurred in the last three years?
Compliance: What regulatory requirements apply? Is the organization currently compliant? Are there any open audit findings?
Technical Assessment
Vulnerability management: When was the last vulnerability scan? What is the patching cadence? Are there known unpatched critical vulnerabilities?
Access controls: How are user accounts managed? Is MFA enforced? Are privileged accounts properly controlled?
Network security: How is the network segmented? Are there intrusion detection systems? Is traffic monitored for anomalies?
Application security: Are applications tested before deployment? What SAST and DAST tools are in use?
Data protection: How is sensitive data classified? Is encryption used at rest and in transit? Are backups tested?
Breach History and Indicators
Known incidents: Request a complete history of security incidents, including scope, impact, and remediation status.
Compromise assessment: Analyze network traffic, endpoint telemetry, and log data for indicators of ongoing or historical compromise. This is the single most valuable security due diligence activity.
Dark web monitoring: Check whether the target's credentials or data appear on dark web markets or forums.
Quantifying Security Risk
Translate findings into financial terms:
- Remediation costs: Investment required to bring security posture to acceptable level
- Compliance costs: Investment to achieve and maintain compliance
- Breach probability: Estimated probability and potential cost of a material breach
- Insurance coverage: Existing cyber insurance policies, limits, and transferability
Post-Acquisition Security Integration
Immediate Actions (Days 1-30)
- Audit and restrict administrative access
- Address critical vulnerabilities identified during due diligence
- Deploy or enhance security monitoring
- Establish incident reporting channels
Near-Term (Months 2-6)
- Extend acquirer's security policies to acquired company
- Integrate identity platforms
- Consolidate security tools
Medium-Term (Months 7-18)
- Align network architecture and security zones
- Harmonize compliance programs
- Build unified security culture through training
The Board-Level Conversation
Cybersecurity risk should be discussed at the board level during every acquisition. What is the security posture? What are the material risks? What is the remediation cost? What is the residual risk? These questions are as important as the financial and commercial questions.
Related posts

From Data Warehouse to AI: Building the Foundation for Machine Learning
How to extend your data warehouse into an ML-ready platform — from feature stores and training data management to real-time feature serving.

Cloud-Native Application Architecture: Patterns That Scale
Essential cloud-native architecture patterns — from twelve-factor foundations and microservice boundaries to event-driven design and resilience engineering.

API Design for Enterprise Systems: Principles That Last
Enterprise API design principles that stand the test of time — from resource modeling and error handling to pagination, security, and lifecycle management.